Signing apps
The External Signing extension enables the workflow to verify the signing credentials and bundle everything you need to sign externally in a zip file, including a script for signing. The workflow then pauses at the signing step to let you take care of signing the app.
The signing step does not sign the app—this page describes the steps you take to download the zip file, sign the app on a local signing server, and upload the signed app before continuing to the next step.
When the app is ready for signing, the workflow status shows that the app is waiting on Signing. This status is available via the Dashboard > Deployment Workflow widget, as well as the workflow run details on App Details page. If you created a notification list when you configured the signing step, the platform sends email to those users when the app is ready for signing.
Signing the app
When the workflow is running and gets to the signing step, it pauses after creating the signing package.
- On the Dashboard, the Deployment Workflow widget shows that the app is waiting on Signing.
- Click Signing to go to the Deployment Status page.
- Click the download button on the Signing step to download the zip file.
- On the local signing server:
- Unzip and sign the app on a local signing server. See Using the signing bundle below.
- On the Blue Cedar Platform after signing the app:
- Back on the Deployment Status page, use the upload button on the Signing step to upload the signed app file.
- The workflow continues to the next step.
Using the signing bundle
The Blue Cedar Platform prepares a signing bundle with the app, a signing script, and all of the signing credentials as configured for the app's workflow. This section describes how to use the contents of the bundle (zip file) to sign the app.
Signing the app on a local signing server
When a workflow includes a Signing step, the platform produces a zip file with these contents:
- The integrated app (.apk or .ipa)
- A script (sign.sh) which calls the codesign script (written in Python)
- The codesign.py script
- A common_utils folder with a set of Python utilities
- Signing credentials as configured in your workflow. These include:
- Android keystore or iOS signing certificate as specified in the signing extension (Extension - Signing)
- iOS provisioning profile specified in a distribution step of the workflow (such as Distribution - Microsoft Endpoint Manager or Distribution - BlackBerry UEM)
If any signing credentials are missing, the script prompts for those files. You can also override the files included in the zip file by specifying new files when you run the script. (See Signing script parameters below.)
Signing server requirements
iOS
Sign iOS apps on a Mac (macOS 10.12+) with Xcode 8.3.2+ and your code signing identity.
Android
Sign Android apps on a macOS or Linux server with Android Studio SDK, including build-tools 29.0.2+. The signing process uses apksigner and zipalign, which are included in the build-tools.
Python
The signing script requires you to have Python 3 installed on your signing server. If needed, download the latest Python 3 here: https://www.python.org/downloads/
Notes:
- MacOS Catalina already has Python 3 installed.
- Signing iOS apps that are using tamper detection will require the installation of the cryptography package from Python. In the Terminal window run this command:
pip3 install cryptographyBuild tools
You may need to confirm that the build-tools location is in your command path. On the Mac signing server, find the installation folder in Android Studio > Configure > SDK Manager. Open a Terminal window and check the path:
$ echo $PATH
/usr/local/bin:/usr/bin:/bin:/usr/sbin:/sbinFind the path to the build-tools under the SDK installation folder, and add it to the search path, for example:
"/Users/jlennon/Library/Android/sdk/build-tools/29.0.3/"
The command below will temporarily add the path to your terminal session, however the $PATH value will be reset after a system reboot
$ PATH=$PATH:/Users/jlennon/Library/Android/sdk/build-tools/30.0.3/To permanently modify the $PATH variable you will need to add your path's to your Mac's configuration file.
For Mac's using the Bash shell you will need to modify the .profile configuration file and for Mac's using the ZSH shell you will modify the .zshrc configuration file.
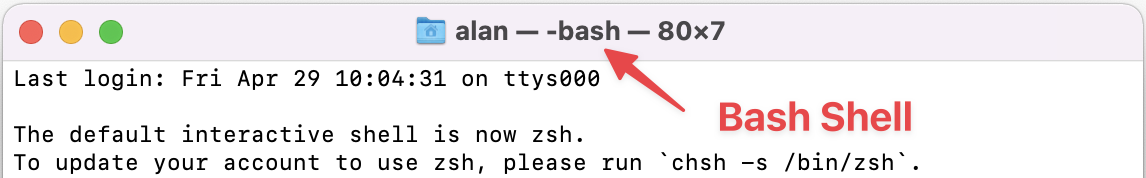
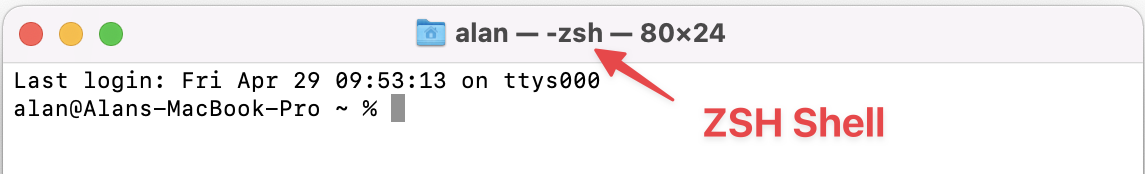
If you are not sure what shell you are using you can launch your Terminal app and view what Shell is loaded. Please see the below images to determine what Shell is currently the default for your OS
The editors installed by default on macOS are nano, vi/vim, and ed. The commands below are for use with the nano editor.
For Bash
$ sudo nano ~/.profile
For ZSH
$ sudo nano ~/.zshrc
Add the following lines to your configuration file, adjusted for your environment's paths
export ANDROID_SDK=/Users/jlennon/Library/Android/sdk
export BUILD_TOOLS_VERSION=30.0.3
export PATH=$PATH:$ANDROID_SDK/platform-tools
export PATH=$PATH:$ANDROID_SDK/build-tools/$BUILD_TOOLS_VERSION
To save your changes in Nano type the following key commands
Ctrl+X
Y
Enter
Reload the configuration profile and validate the $PATH variable is correct
For Bash
$ source ~/.profile
For ZSH
$ source ~/.zshrc
$echo $PATH
To sign the app using the contents of the zip file:
- On your macOS or Linux server, extract the contents of the zip file.
Run the script:
$ sh sign.sh
Optionally, you can specify the output filename
For iOS:
$ sh sign.sh -o output_filename.ipaFor Android:
$ sh sign.sh -o output_filename.apkIf you don't specify an output filename, the signing script displays the filename when complete.
Note: Do not specify the input filename.
If you script does not run you may need to make the sign.sh script executable and rerun the script
In the directory with the extracted files
$ cd exported-com.qwe.myapp
$ chmod +x sign.sh
$ sh sign.shSigning script parameters
Use ./sign.sh to run the signing script as shown above.
To override the signing profile details bundled with the app during integration, you can use the signing script to pass in these parameters.
Android
| Signing script flag | Description |
|---|---|
| -k, --keystore | The location of the keystore to sign the Android app with |
| -a, --alias | The alias for the provided keystore |
| -p, --password | The password for the provided keystore |
| -o, --output | The output location for the signed Android app |
| -c, --custom-app-id | Custom package name for the app |
iOS
| Signing script flag | Description |
|---|---|
| -a, --app | The iOS app you would like to sign |
| -c, --custom-app-id | Custom bundle ID for the app |
| -i, --identity | The signing identity to use for signing |
| -p, --profile | The provisioning profile to sign the app. |
| -e, --entitlements | The signing entitlements to sign the app |
| -o, --output | The output location for the signed iOS app |
